New Charges Derail COVID Release for Hacker Who Aided ISIS
mardi 19 janvier 2021 à 19:39A hacker serving a 20-year sentence for stealing personal data on 1,300 U.S. military and government employees and giving it to an Islamic State hacker group in 2015 has been charged once again with fraud and identity theft. The new charges have derailed plans to deport him under compassionate release because of the COVID-19 pandemic.
Ardit Ferizi, a 25-year-old citizen of Kosovo, was slated to be sent home earlier this month after a federal judge signed an order commuting his sentence to time served. The release was granted in part due to Ferizi’s 2018 diagnosis if asthma, as well as a COVID outbreak at the facility where he was housed in 2020.
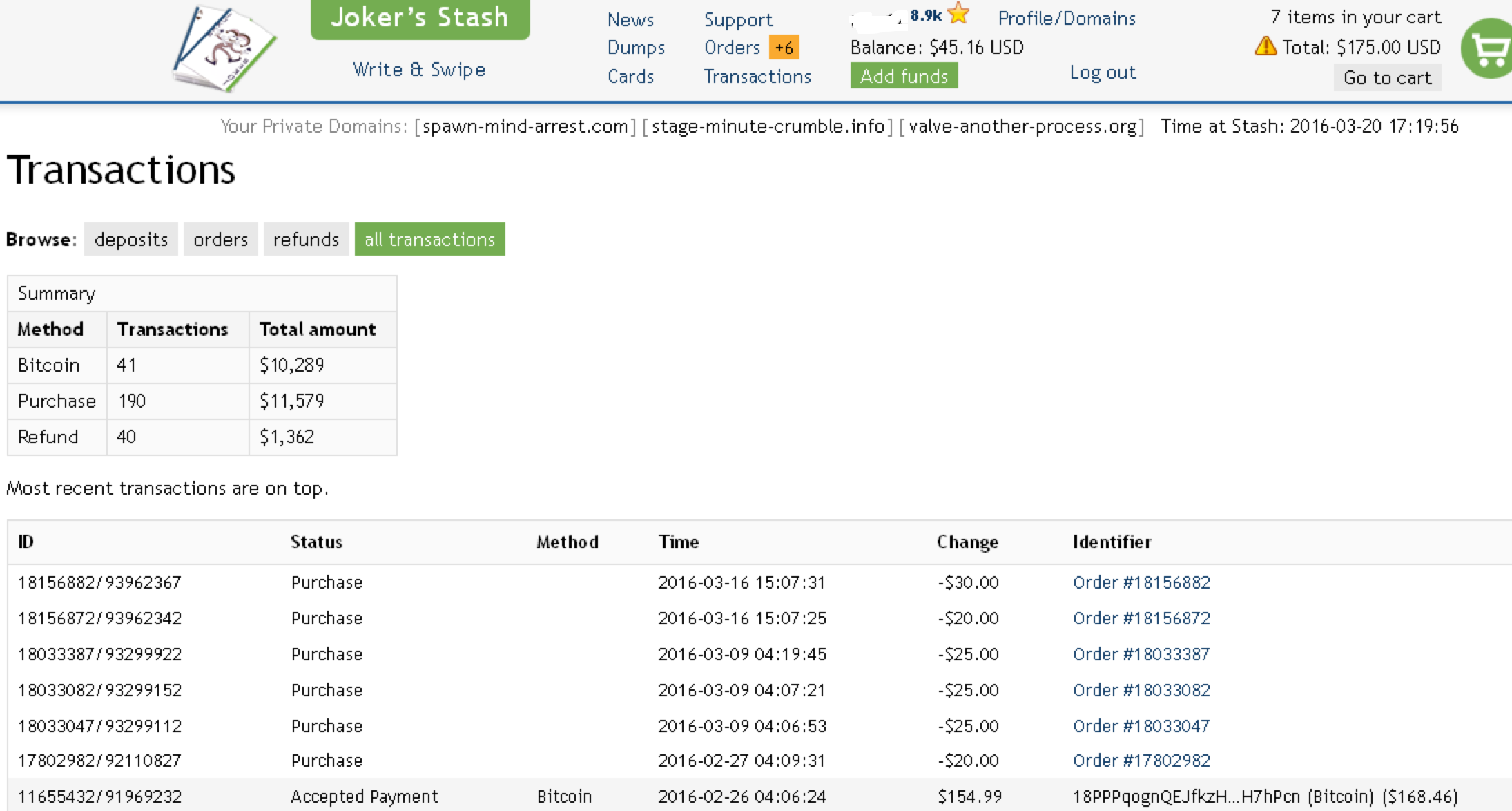
But while Ferizi was in quarantine awaiting deportation the Justice Department unsealed new charges against him, saying he’d conspired from prison with associates on the outside to access stolen data and launder the bitcoin proceeds of his previous crimes.
In the years leading up to his arrest, Ferizi was the administrator of a cybercrime forum called Pentagon Crew. He also served as the leader of an ethnic Albanian group of hackers from Kosovo known as Kosova Hacker’s Security (KHS), which focused on compromising government and private websites in Israel, Serbia, Greece, Ukraine and the United States.
In December 2015, Ferizi was apprehended in Malaysia and extradited to the United States. In January 2016, Ferizi pleaded guilty to providing material support to a terrorist group and to unauthorized access. He admitted to hacking a U.S.-based e-commerce company, stealing personal and financial data on 1,300 government employees, and providing the data to an Islamic State hacking group.
Ferizi give the purloined data to Junaid “Trick” Hussain, a 21-year-old hacker and recruiter for ISIS who published it in August 2015 as part of a directive that ISIS supporters kill the named U.S. military members and government employees. Later that month, Hussain was reportedly killed by a drone strike in Syria.
The government says Ferizi and his associates made money by hacking PayPal and other financial accounts, and through pornography sites he allegedly set up mainly to steal personal and financial data from visitors.

Junaid Hussain’s Twitter profile photo.
Between 2015 and 2019, Ferizi was imprisoned at a facility in Illinois that housed several other notable convicts. For example, prosecutors allege that Ferizi was an associate of Mahmud “Red” Abouhalima, who was serving a 240 year sentence at the prison for his role in the 1993 World Trade Center bombing.
Another inmate incarcerated at the same facility was Shawn Bridges, a former U.S. Secret Service agent serving almost eight years for stealing $820,000 worth of bitcoin from online drug dealers while investigating the hidden underground website Silk Road. Prosecutors say Ferizi and Bridges discussed ways to hide their bitcoin.
The information about Ferizi’s inmate friends came via a tip from another convict, who told the FBI that Ferizi was allegedly using his access to the prison’s email system to share email and bitcoin account passwords with family members back home.
The Justice Department said subpoenas served on Ferizi’s email accounts and interviews with his associates show Ferizi’s brother in Kosovo used the information to “liquidate the proceeds of Ferizi’s previous criminal hacking activities.”
[Side note: It may be little more than a coincidence, but my PayPal account was hacked in Dec. 2015 by criminals who social engineered PayPal employees over the phone into changing my password and bypassing multi-factor authentication. The hackers attempted to send my balance to an account tied to Hussain, but the transfer never went through.]
Ferizi is being tried in California, but has not yet had an initial appearance in court. He’s charged with one count of aggravated identity theft and one count of wire fraud. If convicted of wire fraud, he faces a maximum penalty of 20 years in prison and a fine of $250,000. If convicted of aggravated identity theft, he faces a mandatory penalty of 2 years in prison in addition to the punishment imposed for a wire fraud conviction.